 DK
DK
 DK
DK
Achieve Cyber Essentials and Cyber Essentials Plus certification with a little help from IT Governance, one of the scheme’s founding certification bodies that remains one of the largest in the UK.
Please ensure you select the correct package for your organisation size: this must reflect the total number of employees across the entire organisation, regardless of the certification scope.
![]()
![]()
Some of the Cyber Essentials self-assessment questions can be difficult to understand if you do not have a technical IT background or you have a complex company structure. This service is applicable for the first year of your subscription and provides up to three hours* of one-to-one consultancy support. It’s ideal for organisations that need extra help understanding the scheme, defining the scope of their certification or completing the SAQ.
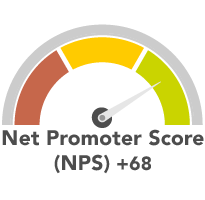
Our Cyber Essentials services have an excellent NPS (Net Promoter Score) of +68.
Our Get A Little Help package has been created for organisations that have some understanding and knowledge of the five key controls required for certification, but that may need some help completing the IASME SAQ.
“Our consultant, Terry Norton, was professional throughout and clearly had a very good knowledge of the standard and the testing, being able to help our IT Administrator ensure the relevant audit tools were installed correctly. We also found Terry friendly, patient and helpful, which is very important for remote sessions.”
- Peter Hodgson, Viewpoint Construction Software Limited
“Professional and supportive, great customer service. Maintained a dialogue without making the candidate feel under pressure with the process. Supportive throughout.”
- Rowan Irwin, T-Systems Limited
“Brilliant service from the team who were completely supportive of someone like me who runs a microbusiness and is hopeless with technical stuff. I am so grateful fo the handholding and advice you gave me.”
- Caroline
“Thanks for all your support, team – really appreciate your assistance in getting us through this in such a short space of time. Couldn’t recommend a better group of folk to work with!”
- Rowan Troy, Six Degrees Technology Group Limited
“Amazing Service, very friendly throughout and willing to help you every step through the process.”
- Ian
“IT Governance were very helpful and really focussed on what was needed to get the certification and have a more secure setup as part of the process (we did not just get assurance, we improved our assurance process).”
- Karl Axnick, Alscient Ltd
“Terry and Dan were extremely helpful, knowledgeable, and provide quick and effective answers to any query I raised.”
- Anonymous
IT Governance is one of the founding Cyber Essentials certification bodies and remains one of the largest in the UK. We have issued more than 6,000 certifications worldwide, and our broad range of fixed-price services has helped thousands of organisations achieve baseline cyber security.
Implementing the five controls correctly will help protect your organisation from approximately 80% of cyber attacks.
The ICO (Information Commissioner’s Office), the UK’s data protection regulator, recommends Cyber Essentials as a “good starting point” for the cyber security of the IT you rely on to hold and process personal data.
Boost your reputation and attract new business by assuring customers you take cyber security seriously and have cyber security measures in place.
Cyber Essentials Plus will give you the opportunity to work with the UK government and MOD.
Cyber Essentials certificates issued in the previous 12 months are listed on the NCSC website, showing suppliers your commitment to protecting your and your customers’ data.
Cyber Essentials Plus involves a technical audit of the systems that are in scope for Cyber Essentials. This includes a representative set of workstations, mobile devices, server devices offering user access to an interactive desktop environment, and build types used by the organisation’s end users to complete their day-to-day duties. The number of builds is defined by the number of configurations of operating systems and software suites installed. If more than one browser or Office suite is used, each variant will need to be tested. If they are installed on the same build, this is acceptable.
All of our Cyber Essentials (and Cyber Essentials Plus) packages include the cost of Cyber Essentials certification, as set out by IASME. Any additional charges above the cost of Cyber Essentials certificate are for consultancy services. The level of consultancy services delivered will vary based on organisation size.
| Size of organisation | Cost of certificate |
|---|---|
| Micro (0–9 employees) | €360 + VAT |
| Small (10–49 employees) | €480 + VAT |
| Medium (50-249 employees) | €540 + VAT |
| Large (250+ employees) | €600 + VAT |
*The amount of consultancy support available depends on the size of your organisation and costs of your certification (set out by IASME).